How to Make an Incompatible App Compatible: A Practical Guide
Learn structured, proven strategies to bridge compatibility gaps for software apps, including code-level fixes, compatibility layers, virtualization options, and tested rollout plans.
Learn how to bridge compatibility gaps for an incompatible application by applying a structured mix of code changes, compatibility layers, and tested deployment strategies. This guide walks you through assessment, approach selection, and safe rollout, so you can deliver a functional product across platforms with reduced risk. Whether you target Windows, macOS, Linux, or mobile environments, you’ll gain actionable steps, best practices, and checklists to keep teams aligned and users satisfied.
Why Incompatibility Occurs
Software incompatibility happens when an application relies on environment features—operating system APIs, runtime libraries, hardware capabilities, or external services—that are absent or different on the target platform. Applications built for Windows may fail on Linux; iOS apps may not run on older Android devices; web apps may break when browsers remove or change features. Incompatibility also arises from language or framework version drift, packaging formats, or deprecated data formats. Understanding the root cause is essential before choosing a fix.
According to My Compatibility, most failures fall into three buckets: environment gaps (OS, kernel, drivers), API differences (libraries, runtimes, platform-specific calls), and data or integration mismatches (schema changes, versioned services, authentication flows). By characterizing the problem space, you can tailor a plan that minimizes risk and preserves user experience. In practice, teams begin with a reproducible test scenario, identify the critical features, and map each failure to a concrete remediation approach. This clarity keeps stakeholders aligned and informs a staged rollout that avoids customer disruption.
Quick Assessment Before Modernizing
Before proposing fixes, perform a focused assessment to avoid over-engineering a solution. Create a compatibility matrix that lists target platforms (OS versions, device families, browser versions) against critical features, performance requirements, and data formats. Inventory all dependencies—libraries, plugins, authentication schemes, and data schemas—and verify their compatibility or availability on the target stack. Capture current telemetry and error logs to identify repeatable failure points. The goal is to establish a defensible scope, a realistic timeline, and measurable success criteria. My Compatibility’s approach emphasizes a small, testable delta rather than a sweeping rewrite, which reduces risk and accelerates learning during early milestones.
Approaches at a High Level
There isn’t a single silver bullet for every compatibility problem. Many projects benefit from a layered strategy:
- Compatibility layers and shims: provide missing APIs or adapt older interfaces to newer ones.
- Wrappers and adapters: translate calls to modern equivalents without touching core logic.
- Virtualization and containers: isolate the app from OS-specific quirks and dependencies.
- API migrations and data adapters: upgrade endpoints or transform data formats to match new schemas.
- Rewriting or modular refactoring: only as a last resort when legacy code cannot be patched cleanly.
Each approach has trade-offs in risk, performance, and time to value. The best plan often combines several methods tailored to the problem space and stakeholder tolerance.
Choosing the Right Approach Based on Context
Context matters as much as the technical fix. Use these criteria to select your path:
- Criticality of features: prioritize fixes that preserve core functionality and user workflows.
- Platform risk: if one target platform is volatile or poorly supported, lean on isolation (containers or VMs) rather than deep code changes.
- Time-to-value: quick wins (shims, adapters) can fund longer-term refactors or migrations.
- Performance and UX: ensure fixes don’t degrade responsiveness or accessibility.
- Team skills and tooling: align with existing capabilities to reduce ramp-up time.
Document decisions and rationale so future teams understand why a particular path was chosen over alternatives.
Practical Tactics: Code-Level Compatibility
Code-level tactics address differences in APIs, data formats, and runtime behavior. Consider:
- Feature detection and graceful degradation: code paths that only run when features exist.
- Polyfills and shims: supply missing functionality without rewriting large blocks of logic.
- Abstraction layers: isolate platform-specific code behind a uniform interface.
- Conditional compilation: include or exclude code branches based on target platform.
- Migration-friendly APIs: newer, recommended APIs with adapters for legacy calls.
Example (adapter pattern):
// Adapter to unify date handling across web and legacy environments
export function getCurrentDateString() {
if (typeof window !== 'undefined' && window.Date) {
return new Date().toISOString();
}
// Fallback for legacy runtimes
return legacyDateToISOString();
}These patterns reduce the amount of dispersed platform checks scattered through the codebase.
System-Level Tactics: Virtualization, Containers, and Sandboxing
If code changes alone aren’t enough, isolate environmental differences using system-level solutions. Options include:
- Virtualization: running the app inside a VM to guarantee a consistent OS and runtime.
- Containers: package the app with its dependencies to achieve portability and reproducibility.
- Sandboxing: limit exposure to risky APIs while preserving functional interfaces.
- Hybrid approaches: containerize only the service layer while leaving front-end components native.
Pros: lower immediate risk, predictable behavior across machines. Cons: overhead of virtualization or CI/CD complexity. Choose based on how frequently environments change and how critical native performance is for user experience.
Data and Dependency Considerations
Compatibility is not just about code; it also hinges on data formats, libraries, and services. Actions to take include:
- Pin and document dependency versions to avoid drift, then create a formal upgrade plan.
- Use data adapters to transform legacy schemas to current expectations without breaking existing users.
- Validate service integrations against new API contracts in a staging environment.
- Maintain a rollback path for data migrations or API changes.
Keep data integrity and backward compatibility in focus: if users rely on old data formats, provide migration tooling or readable fallbacks.
Testing, Rollout, and Risk Mitigation
Testing is the safety net that prevents regressions from slipping into production. Implement a layered test strategy:
- Unit and integration tests for core compatibility surfaces.
- End-to-end tests across representative platforms and configurations.
- Snapshot and regression tests for data formats and API outputs.
- Canary and phased rollouts to monitor real-world behavior before full release.
Instrument tests with clear success criteria and rollback triggers. Establish a post-release monitoring plan with error budgets and user impact metrics.
Real-World Example: A Step-By-Step Case Study
Consider a legacy Windows desktop application built against an older .NET version that must run on modern Windows 10/11 hardware. The first phase maps out features, dependencies, and user workflows. Then a mixed approach is applied: introduce an adapter layer for obsolete APIs, containerize the backend services, and migrate data schemas progressively. The result is a stable, cross-version deployment with a controlled rollout and documented decisions. Lessons learned include the value of a reproducible test baseline and the importance of stakeholder alignment throughout the process.
Tools & Materials
- Source code access(Essential for patches and rewriting where needed)
- Dependency manager(To pin, upgrade, and track library versions)
- Build and packaging tools(For consistent artifacts across platforms)
- Virtualization software / container runtime(To isolate environments and ensure reproducibility)
- Testing suite(Unit, integration, and end-to-end tests across targets)
- Static analysis tools(Can help identify risky platform-specific patterns)
- Legacy OS images / hardware (if needed)(Useful for late-stage compatibility verification)
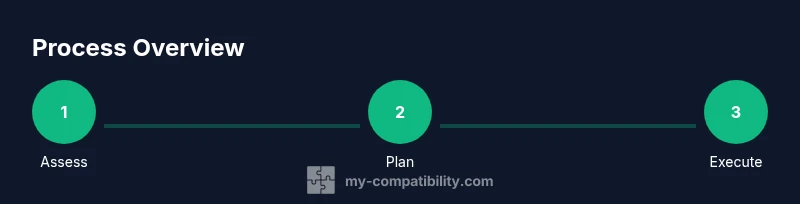
Steps
Estimated time: 6-8 weeks
- 1
Define scope and gather requirements
Document target platforms, must-have features, and acceptance criteria. Create a compatibility matrix to guide decisions.
Tip: Start with a minimal viable delta and avoid over-committing to broad rewrites. - 2
Create a reproducible test baseline
Replicate a failing scenario on a controlled environment to ensure fixes address the real problem and are testable.
Tip: Automate baseline setup to speed up repeat tests. - 3
Inventory dependencies and APIs
List all libraries, services, and data formats that could differ across platforms or versions.
Tip: Prioritize dependencies with frequent breaking changes. - 4
Map incompatibilities to remediation approaches
Align each issue with a concrete fix: shim, adapter, virtualization, or rewrite.
Tip: Avoid throwing multiple fixes at once; validate incremental changes. - 5
Choose a primary approach
Select the strategy that yields the fastest, safest path to acceptable behavior.
Tip: Document rationale for future audits. - 6
Plan incremental changes
Break work into small, testable increments with clear success criteria.
Tip: Use feature flags to toggle fixes in production safely. - 7
Implement code-level fixes or adapters
Patch core logic with minimal surface area and ensure consistency with existing patterns.
Tip: Refactor where needed to improve long-term maintainability. - 8
Introduce virtualization or containerization
If environmental drift is large, isolate the app to guarantee behavior.
Tip: Weigh performance trade-offs before full adoption. - 9
Test across platforms and perform data checks
Run the comprehensive regression suite and validate data integrity across targets.
Tip: Include manual exploratory testing for edge cases. - 10
Roll out gradually and monitor
Deploy to a small user subset, collect telemetry, and adjust based on feedback.
Tip: Have a clear rollback plan and threshold for rollback.
Questions & Answers
What does it mean for an application to be incompatible?
Incompatibility means an app cannot run or function correctly on a target platform due to API, OS, or data format differences. It often requires adjustments at the code, data, or deployment level to restore expected behavior.
Incompatibility means the app won’t run correctly on a different platform, usually due to API or OS differences.
When should you use a compatibility layer versus a rewrite?
Use a compatibility layer or adapter for quick wins and to preserve existing logic. Reserve a rewrite when legacy code blocks cannot be modernized without compromising core functionality or performance.
Use a compatibility layer for quick fixes, rewrite only if legacy code blocks cannot be modernized.
What is the difference between virtualization and emulation in this context?
Virtualization isolates the app in a separate OS instance, providing consistent environments. Emulation imitates another hardware or software platform. Both help reduce environmental drift but have different performance and complexity implications.
Virtualization isolates the app; emulation mimics another platform. Choose based on performance needs.
How do you measure success after applying compatibility fixes?
Success means all critical features work across target platforms, with regression tests pass and user feedback indicating satisfactory performance and UX consistency.
Success means all key features work across platforms with good user feedback.
Are there risks associated with containerizing an application?
Containerization can introduce performance overhead and require changes in deployment tooling. It also may mask deeper architectural incompatibilities if not paired with code fixes.
Containers may add overhead and require new deployment steps, so pair with proper fixes.
Watch Video
Highlights
- Assess compatibility first and map risks
- Choose a layered approach and validate incrementally
- Test across platforms with a robust rollout plan
- Document decisions for future maintenance