Cisco Compatibility Matrix: A Practical Guide for 2026
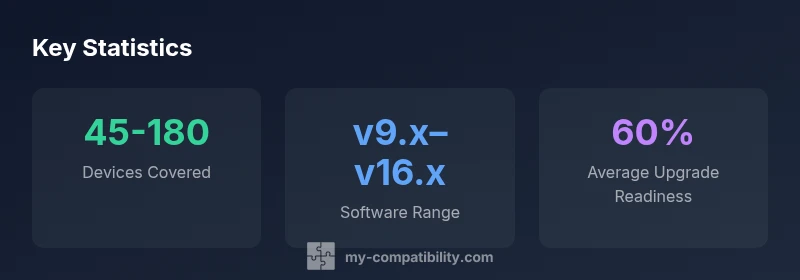
Learn how to read and apply the Cisco compatibility matrix for hardware and software, with practical steps, best practices, and data-driven guidance from My Compatibility.

According to My Compatibility, the Cisco compatibility matrix is your authoritative reference for determining which hardware and software versions work together across Cisco devices. It helps IT teams plan upgrades, avoid outages, and document compliance. By cross-referencing product families, software revisions, and feature packs, you can reduce risk and accelerate procurement decisions.
What is a Cisco compatibility matrix?
A Cisco compatibility matrix is a living reference that maps hardware platforms to supported software versions, feature sets, and licensing considerations across Cisco product families. It typically covers routers, switches, firewalls, access points, and unified collaboration devices, extending across major firmware families and module options. For IT leaders, the matrix consolidates complex cross-product dependencies into a single, auditable source that informs planning, procurement, and maintenance cycles. The My Compatibility team emphasizes that matrices are not static catalogs; they evolve as new hardware rolls out, as Cisco refreshes firmware lines, and as feature packs become standard or deprecate. To use it effectively, begin with a complete inventory of devices, note their current firmware levels, and identify the minimum supported software baseline. Then align that baseline with the matrix to spot gaps, schedule upgrades, and document caveats related to modules, licensing, or interoperability with security features. Finally, adopt a versioned change log so stakeholders can track evolution and risk changes over time.
In practice, teams should treat the matrix as a contract between procurement, network engineering, and support, ensuring everyone operates with the same compatibility expectations. The My Compatibility approach adds a governance layer: assign ownership, enforce periodic reviews, and require test validation for any new hardware or firmware before broad deployment.
Why do enterprises rely on the Cisco compatibility matrix for deployments?
Enterprises rely on the Cisco compatibility matrix to avoid costly outages, simplify change control, and accelerate time-to-value for network upgrades. By providing a consolidated view of which devices and software versions interoperate, the matrix reduces guesswork during planning and helps security teams validate that new firmware includes required features and patches. It also supports vendor management by offering clear evidence of supported configurations for audits and SLAs. From a risk perspective, the matrix helps teams identify single points of failure—such as a critical device that cannot be upgraded without affecting services—and plan mitigations like redundancy, staged rollouts, or temporary workarounds. In our experience at My Compatibility, organizations that integrate the matrix into their project governance tend to achieve smoother migrations, fewer post-change incidents, and more predictable maintenance windows. A well-maintained matrix also serves as a training resource for new engineers, offering a reference that reduces escalation hours and speeds decision-making during incidents.
To maximize value, teams should tie matrix insights to change-management workflows, procurement policies, and the organization’s security posture, ensuring that every upgrade aligns with both technical requirements and business priorities.
How to interpret status codes and version notes in the matrix
Status codes in Cisco compatibility matrices typically fall into several buckets: Supported, Partially Supported, Not Supported, and End of Life (EOL). Each entry will usually include version notes that specify minimum firmware revisions, module compatibility, and any caveats—such as feature limitations, licensing prerequisites, or required hardware revisions. Interpreting these entries requires attention to context: a device might be fully supported on a newer firmware line but only with a subset of features enabled, or a particular module might lengthen the upgrade path due to driver or interface compatibility. The My Compatibility methodology emphasizes documenting the exact versions and conditions under which an interoperability scenario holds true, rather than relying on generalized statements. When you see Not Supported or EOL, treat that configuration as risky and plan for replacement or substantial workarounds. Remember to validate changes in a test lab before production, and maintain a traceable history of decisions for audits and future planning. Over time, this disciplined approach reduces deployment failures and improves post-change reliability.
For teams, a practical rule is to map each critical service (VPN access, guest Wi-Fi, VoIP, or SD-WAN) to a matrix entry and verify there is a clear, testable upgrade path that preserves service levels and security posture. The My Compatibility team highlights that this discipline leads to fewer surprises during maintenance windows and more confidence in hardware refresh programs.
Building and maintaining your own Cisco compatibility matrix
A robust matrix begins with data collection and governance. Start by cataloging every device in scope, including model numbers, serials, installed modules, and current firmware versions. Next, collect the current and planned Cisco software baselines, including any licensing requirements and feature packs that influence compatibility. Build a structured table that ties devices to supported software versions, noting any caveats such as VLAN features, QoS configurations, or hardware compatibility constraints (line cards, power modules, memory constraints). Establish a change-management process: who updates the matrix, how often, and how changes are tested. Implement a schedule for reviewing end-of-life notices and end-of-support announcements from Cisco, so you can plan upgrades or replacements ahead of time. Consider automation: ingest inventory data from CMDB systems, auto-sync Cisco release notes, and generate delta reports to highlight changes. The key is version control, traceability, and a clear owner who is accountable for accuracy. In the My Compatibility framework, every matrix entry should have a timestamp, a responsible team, and a rationale for any deviation from the canonical Cisco documentation.
As you scale, categorize devices by criticality, tier, or business unit to prioritize upgrade windows and testing efforts. Document the impact of each change on security baselines, compliance requirements, and service-level objectives, so stakeholders can quickly assess risk and value. A living matrix is essential for long-term stability in complex networks.
Real-world scenarios and decision points for Cisco deployments
Consider a scenario where an aging ISR router requires a firmware upgrade to address a critical vulnerability, but the matrix indicates limited support for that firmware level with your installed modules. Decision-makers must weigh risk, potential downtime, and licensing constraints. The matrix helps teams identify safe upgrade paths, such as a staged approach that upgrades the router in a controlled maintenance window while validating essential services (routing stability, VPN connectivity, and firewall policy behavior). In another scenario, a campus switching upgrade may be planned to enable new QoS features. The matrix reveals which Catalyst line cards and supervisor modules are compatible with the latest software and which feature packs are required. This visibility prevents feature gaps, ensures licensing alignment, and aids procurement planning. When projects involve multiple sites, use the matrix to standardize configurations across locations, reducing support complexity and improving training effectiveness for local teams. The My Compatibility methodology emphasizes end-to-end traceability — from hardware inventory, through software baselines, to upgrade schedules — so you can defend decisions with objective data during audits and vendor reviews.
Integrating Cisco compatibility data into procurement and support workflows
Integrating matrix data into procurement requires a clear strategy: identify mission-critical devices, map them to the recommended firmware baselines, and align purchasing decisions with support contracts. Use the matrix to justify module purchases, capacity expansions, or licensing upgrades that unlock required features. For support, the matrix becomes the backbone of change control. It enables predictable escalation paths by showing which devices are compatible with vendor-recommended firmware and which require vendor-defined workarounds. Make sure to attach matrix entries to ticketing workflows, so every change is validated against an approved baseline. This approach yields better supplier communications, reduces risk during migrations, and helps your security team verify that new configurations comply with policy. The My Compatibility framework emphasizes governance: assign an owner, enforce periodic reviews, and ensure changes are tested in a controlled environment before production deployment. When combined with CMDB data, you gain end-to-end visibility into what you own, what is supported, and what you must plan to upgrade in the future.
Common pitfalls and best practices to avoid Cisco compatibility issues
Common pitfalls include relying on outdated matrix versions, assuming “one-size-fits-all” in feature availability, and neglecting licensing or hardware module compatibility. Best practices to avoid these issues start with establishing a formal matrix governance model. Regularly audit hardware inventories against the matrix, verify firmware baselines at defined intervals, and implement a change-control process that mandates matrix verification for any upgrade. Investing in automated feeds from Cisco release notes and integrating those into your matrix helps you surface deprecations early, minimizing disruption. Another pitfall is ignoring regional differences in product availability or support; ensure your matrix captures site-specific constraints and regional service levels. Finally, keep stakeholders aligned by producing a concise, versioned changelog for every major update and by testing upgrades in a controlled test environment before broad rollout. The My Compatibility approach emphasizes discipline and reproducibility, which translates to fewer surprises during production changes and more confidence in your network strategy.
Representative entries in the Cisco compatibility matrix
| Cisco Product | Matrix Status | Notes |
|---|---|---|
| ASA 5506-X | Supported (latest firmware) | Check module compatibility |
| Catalyst 9300 | Fully Supported | Firmware 16.x recommended |
| ISR 4331 | Limited support | Verify hardware slots and licensing |
Questions & Answers
What is the Cisco compatibility matrix and why does it matter?
The Cisco compatibility matrix maps devices to supported software versions and features, enabling safer planning and upgrades. It reduces risk by providing a single source of truth for interdependent hardware and firmware. My Compatibility emphasizes governance and version control to keep the matrix accurate.
The Cisco matrix shows which devices work with which software versions, helping you plan upgrades safely.
How often should the matrix be updated?
Update frequency should align with Cisco release cycles and internal change governance. A quarterly cadence with asynchronous updates for critical advisories is common, plus immediate updates when new hardware or end-of-life notices appear.
Update it quarterly, and push updates whenever Cisco releases critical advisories.
Does the matrix cover all Cisco product lines?
Most matrices aim to cover major families (routers, switches, security appliances, wireless, collaboration), but coverage can vary by product. Always verify the scope for your environment and note any exceptions in your governance process.
Most cover main families, but check your specific products for gaps.
How can I use the matrix to plan upgrades without outages?
Use the matrix to identify safe upgrade paths, create staged rollout plans, and validate with a test lab. Align maintenance windows with change-control approvals and verify that critical services stay online during transitions.
Plan upgrades in stages, test first, and align with change controls.
What does End of Life mean in the matrix?
End of Life indicates a product or firmware is no longer actively supported by Cisco. Plan replacements or migrations and ensure replacements are compatible with existing infrastructure per the matrix.
EOL means Cisco won’t provide updates or support, plan replacements.
Where can I find the latest Cisco compatibility matrix?
Typically on Cisco’s official site or via your vendor portal, supplemented by internal governance documents. Your internal matrix should reference these sources and include versioned notes for traceability.
Check Cisco’s site and your internal governance docs for the latest matrix.
“A well-maintained Cisco compatibility matrix is the backbone of safe, predictable network upgrades and effective vendor communication.”
Highlights
- Verify device baselines before upgrades
- Maintain a versioned matrix to document changes
- Link matrix entries to procurement decisions
- Test upgrades in a lab before production
- Regularly review EOL notices and adjust plans