evm compatible vs equivalent: A comprehensive comparison
An in-depth comparison of evm compatible vs equivalent, covering compatibility layers, migration pain points, performance implications, and practical guidance for developers.

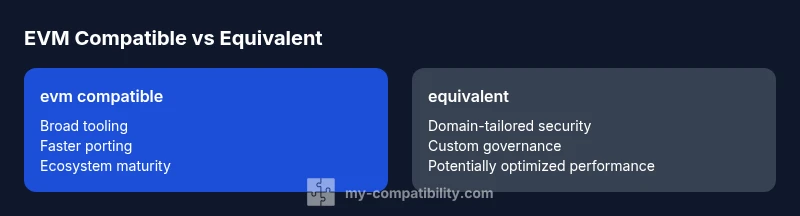
In most cases, evm compatible solutions offer broader ecosystem support and easier porting, while an equivalent approach prioritizes bespoke tooling and tighter security boundaries. The right choice depends on migration goals, cost, and risk tolerance. This TL;DR outlines when each path shines and what trade-offs to expect.
What 'evm compatible' means in practice
In the context of blockchain platforms, evm compatible means the platform aims to run Ethereum Virtual Machine bytecode and support the Solidity language and existing Ethereum tooling with minimal adaptation. This enables developers to port smart contracts, libraries, and dApps with reduced rewrite effort. The term also covers ABI compatibility, gas semantics alignment, and access to Ethereum-style wallets and explorers. When evaluating evm compatible options, teams consider how fully they reproduce EVM semantics, whether they support common opcodes, and how behavior matches expectations across networks. In practice, pursuing evm compatible paths often hinges on ecosystem leverage, interoperability with bridges, and access to established security patterns. According to My Compatibility analysis, alignment with Ethereum tooling often shortens timelines for deployment and reduces learning curves for developers, though depth of support can vary by project and target chain. The keyword evm compatible vs equivalent surfaces here as a central consideration for migration planning and architecture design.
This block continues the exploration of how organizations think about compatibility in practical terms. It highlights how the EVM surface area—opcodes, gas rules, and contract ABI behavior—influences porting effort, tooling availability, and risk handling. Readers will see why the My Compatibility team emphasizes ecosystem maturity as a decision driver, especially for teams transitioning from Ethereum or those bridging to other chains. The discussion also frames common traps—such as assuming full parity without auditing opcode behavior across networks—so readers can plan mitigations early.
Core differences at a glance
- EVM-compatible models prioritize immediate leverage of Ethereum tooling, libraries, wallets, and developer skills. They tend to deliver faster go-to-market for smart contracts and dApps.
- Equivalent architectures emphasize architecture-specific optimizations, security postures, and sometimes custom languages or VMs designed to meet domain requirements more tightly. They may incur longer development cycles but can yield stronger domain alignment and security guarantees.
- The “evm compatible vs equivalent” decision often hinges on whether you value ecosystem momentum over bespoke control. My Compatibility’s research shows that teams with strong Ethereum experience usually pursue evm compatibility first, while those in regulated industries may prefer an equivalent setup and tailor-made controls.
Let’s translate this into concrete planning steps for teams evaluating both paths.
Comparison
| Feature | evm compatible | equivalent |
|---|---|---|
| EVM instruction compatibility | High with broad opcode support | Custom or partial compatibility; some opcodes may be unavailable |
| Solidity support | Full Solidity, libraries, and tools | Partial or alternative language tooling; potential porting gaps |
| Tooling ecosystem | Extensive (ethers.js, Hardhat, wallets, explorers) | Smaller ecosystem; bespoke toolchain required |
| Security model alignment | Mature patterns; shared security models | Custom risk controls; bespoke threat modeling |
| Migration effort | Low to moderate for contracts and assets | Medium to high due to rewrites and audits |
| Upgradeability/governance | Standard upgrade paths; ecosystem norms | Custom governance models; longer maturation |
| Performance considerations | Solid performance with mature optimizations | Variable; depends on abstraction layer and VM design |
| Total cost of ownership | Lower initial cost due to ecosystem and tooling | Higher due to bespoke components and audits |
Positives
- Access to large Ethereum tooling and developer ecosystem
- Faster deployment by leveraging familiar patterns
- Lower learning curve for teams already in Ethereum space
- Better interoperability with bridges and analytics
Cons
- Potential for ecosystem dependency or vendor lock-in
- Possible reduced opportunity for deep, custom optimizations
- Security surface area from compatibility layers if not carefully managed
- Migration can still incur non-trivial audit and testing costs
EVM-compatible generally wins for broad interoperability; equivalent architectures win when security tailoring and customization are paramount.
For most teams, starting with evm-compatible architectures provides faster access to a mature ecosystem and faster deployment. If your project has strict security, regulatory, or domain-specific needs, an equivalent approach may offer better long-term control and tailored protections. My Compatibility’s verdict is to assess goals early and pilot both approaches where possible.
Questions & Answers
What does it mean for a platform to be evm compatible?
EVM compatibility means the platform can execute Ethereum smart contracts, support Solidity tooling, and reproduce Ethereum-like semantics such as ABI behavior and gas rules. It enables developers to port existing contracts with minimal rewrites and access a large ecosystem of libraries, wallets, and debugging tools.
EVM compatibility lets a platform run Ethereum contracts and use familiar Solidity tooling, making porting easier and unlocking a vast ecosystem.
What does an 'equivalent' architecture entail?
An equivalent architecture aims to mimic the functional behavior of the EVM without relying on a direct EVM implementation. This can involve a custom VM, proprietary bytecode, or tailored safety and performance features designed to meet specific domain requirements.
An equivalent architecture uses its own VM or bytecode while trying to reproduce key Ethereum behaviors under its own security and performance rules.
Which path is better for migrating existing dApps?
If you need rapid migration with existing codebases and tooling, evm compatibility is typically the faster route. If you require strict, customized security controls or domain-specific features, an equivalent path may be preferable despite a longer ramp-up.
For quick migrations, go with evm compatibility; for custom security and domain needs, consider an equivalent approach.
How do performance and security differ between the two?
EVM-compatible platforms often benefit from mature security patterns and community-reviewed practices. Equivalents can tailor security to risk profiles and may reduce exposure by removing unnecessary abstractions, but require bespoke audits and ongoing governance.
Performance can be solid with both, but equivalents may optimize for security and domain-specific risk, while EVM-compatible options lean on established patterns.
What are typical migration costs I should plan for?
Costs include code rewrites or adapters, security audits, and testing across networks. Evn compatible paths tend to incur lower upfront costs due to existing toolchains, while equivalent approaches may require more extensive audits and governance setup.
Expect audits, testing, and potential rewrites; compatibility paths usually cost less upfront than bespoke equivalents.
Highlights
- Start with evm compatibility to maximize ecosystem access.
- Assess migration cost and risk early in planning.
- Prioritize security design and threat modeling for
- Plan a small-scale pilot to validate assumptions before full rollout.